On This Page
Adding Check Point R8x SmartCenter Server Devices
Overview
You must configure the Check Point servers in the following order: Provider-1 MDS, Provider-1 CMAs, SmartCenter servers (SMCs), and Log Servers (CLMs).
After you upgrade a monitored Check Point SmartCenter device to R80.x, you must upgrade the device in TOS Aurora to use Check Point R8x support.
Prerequisites
Enable a SmartCenter (SMC) Device
You will need to complete the following prerequisite steps to add Check Point SmartCenter devices to TOS Aurora:
- Configure the Check Point server for OPSEC communication with TOS Aurora.
-
Configure the Check Point device to use your TOS Aurora server as a GUI client.
The TOS Aurora server is displayed in a revision in the GUI client column.
- For SMC devices, enable the API software blade.
-
Create a Check Point user with Rest API Access to retrieve revisions:
-
TOS Aurora uses Check Point APIs to connect to (and monitor) Check Point R80.x devices. A user with the SmartCenter Manager or Domain Manager profile who has the Read Only All Permission Profile configured for All Global Domains with the required collection access via the Check Point APIs can retrieve revisions for the device. On an SMC or a CMA:
-
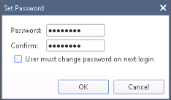
To maintain the password you defined for the Check Point user with REST API access, in Set Password, uncheck User must change password on next login.
-
What Can I Do Here?
Configuring TOS Aurora to Monitor the Policy Revisions of a Check Point Device
-
In TOS Aurora, go to Monitoring
 > Manage Devices.
> Manage Devices. -
Select the appropriate device type.
-
Configure the device settings:
Depending on the Check Point server type, some or all of the following options will appear:
-
Device Type: Check Point SmartCenter
- Name for Display
-
Domain: Available only if you have configured your system for managing multi-domains and All Domains is currently selected. Select the domain to which to add the device. The Domain can only be entered when adding a device; to change the Domain, you must migrate the device.
-
Get revisions from: One of the following:
- IP Address: Revisions are retrieved automatically
- Offline File: (If available) Revisions are manually uploaded to TOS Aurora for Offline Analysis
This option is not available for R80.x SMC devices
-
ST server: In a distributed deployment, select which TOS Aurora cluster monitors this device (not shown in image)
-
Usage Analysis: Select the relevant options:
- Collect traffic logs for rule usage analysis: Necessary for Rule Usage reports.
- Collect traffic logs for object usage analysis : Necessary for reporting on unused objects and services in Rule Usage Reports.
Object usage analysis requires plenty of free disk space (depending on the number of gateways and the amount of traffic logs generated). If disk space is limited, you can configure TOS Aurora to limit the number of days that data is kept.
We recommend that you enable TOS Aurora administrative alerts, which notify you if there is low disk space on the server. When disk utilization exceeds 90% in the partition that has the database, TOS Aurora sends an alert.
-
Enable Topology: Collects routing information for building the network Interactive Map.
Topology options for Advanced management mode are configured when you import managed devices. -
Check Point SMC Version: Select the Check Point version installed on the SMC:
- Version R77 or earlier
- Version R80.x
After you save the device configuration, you cannot change this setting.
-
- Click Next.
-
Configure OPSEC Secure Internal Communication (SIC):
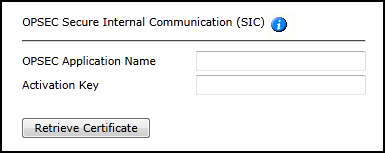
- Enter TOS Aurora's OPSEC Application Name as you defined it for this Check Point server (case sensitive).
- Enter the Activation Key as defined when the OPSEC object was created.
-
Click Retrieve Certificate to setup encrypted communication between TOS Aurora and the Check Point device.
The certificate appears, and the following message is displayed:

- Click Next.
-
In the OPSEC Settings:

- Select Custom.
-
Configure the LEA Authentication fields:
- Authentication Mode: Some options require you to enter an SL or FWN1 Secret Key in the Authentication Keys section and Establish Authentication Key.
- Port
-
Configure the CPMI Authentication fields:
- Authentication Mode
- Port
- Click Next.
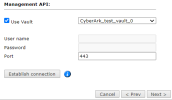
- For SmartCenter devices with R8x, in the Management API settings:
- Enter the credentials for an administrator on the Check Point device. To use a vault server that contains access credentials, select Use Vault and select the server. For more information, see Configuring a Vault Server.
- Enter the port that the Check Point device uses for REST API connections.
- Click Establish Connection to setup encrypted communication between SecureTrack and the Check Point device. The certificate appears, and the following message appears:

-
Click Next.
-
In the Monitoring Settings, do one of the following:
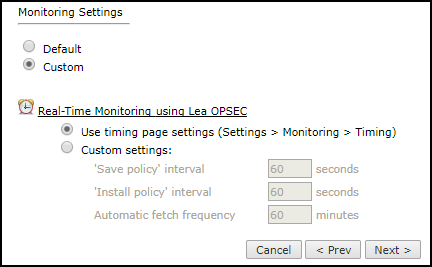
- To use timing settings from the Timing configuration for this device, select Default.
-
To define specific timing settings for this device, select Custom, then select Custom settings, and configure:
- 'Save policy' interval: When a Save Policy event is followed within this time interval by an Install Policy event for the same policy, TOS Aurora tries to combine the two events into a single revision. The default value is 60 seconds.
- 'Install policy' interval: When two or more Install Policy events for the same policy occur within this time interval, TOS Aurora combines the events into a single Install Policy revision (Default: 60 seconds)
- Automatic fetch frequency: Frequency (in minutes) for automatic fetch
- Click Next.
-
You can test the communication with the Check Point server by clicking Test Connectivity:
-
Click Save.
The Check Point device is shown in the Device Configuration list.
If you use non-standard LEA authentication, see Non-Standard LEA Authentication.
- If you have a secondary Check Point management server, configure TOS Aurora to communicate with the secondary server in the event of a failover.
Define an Internet Object
To customize the device object that represents the Internet, see Define Internet Object.
How Do I Get Here?
In TOS Aurora, go to Monitoring ![]() > Manage Devices.
> Manage Devices.