On This Page
Configuring a VMware NSX-T Device to Send Syslogs
|
|
This topic is intended for TOS Administrators. |
Overview
Configure the NSX Manager to send change logs to SecureTrack to receive revisions when firewall rules are changed.
Syslog traffic must be configured to arrive to the TOS cluster that monitors the device - see Sending Additional Information via Syslog.
Define SecureTrack as a Syslog Server
-
Login to the NSX Manager CLI.
-
Run the following command:
set logging-server <host>:514 proto udp level info messageid <messageid> [structured-data update="true"]Use the parameters as follows:
Parameter Description <host>Host name or IP address of the SecureTrack server or Syslog-VIP <messageid>Use "FIREWALL"for imperative APIs, or"-"(dash) for declarative APIsstructured-data(Optional) Recommended for enhanced log filtering and parsing
For more information, see official VMware documentation: Configure Remote Logging and Log Message IDs.
Configure ESXi to Send Syslogs
To receive firewall rule logs from NSX Distributed Firewall, you must also configure the underlying ESXi hosts to forward syslogs to SecureTrack.
ESXi CLI
-
Connect to the CLI of the ESXi server.
-
Enable the syslog service:
-
Set the syslog server (use the Syslog-VIP or external load balancer IP, depending on your TOS configuration):
-
Restart the syslog service:
NSX UI (NSX 3)
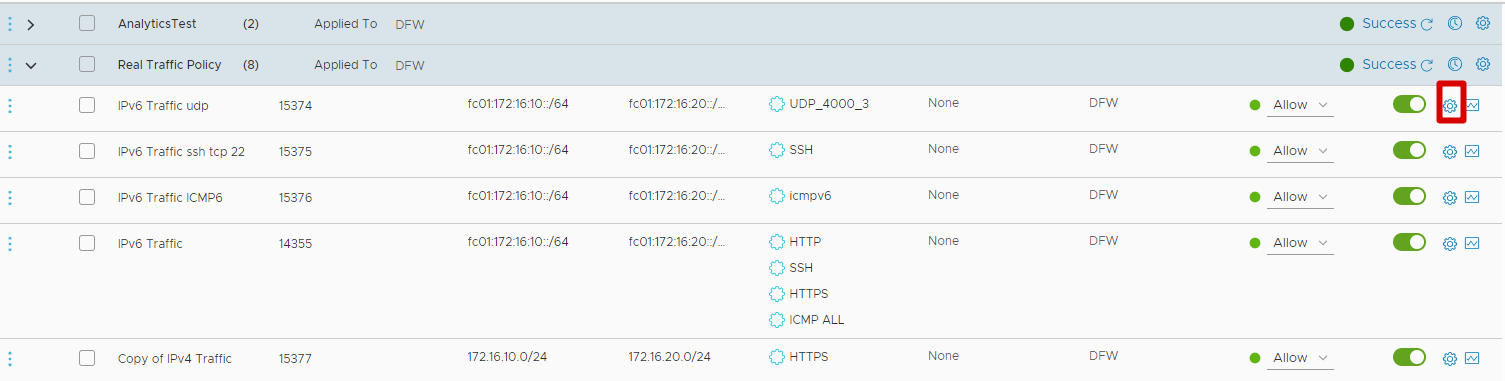
Use the NSX UI to enable logging for individual Distributed Firewall rules.
-
Click the Security tab at the top of the screen.
-
Click Distributed Firewall under East West Security in the left navigation panel.
-
Select a firewall rule you want to monitor.
-
Click the settings (cogwheel) icon next to the rule.
The Settings window opens.
-
Turn on the Enable toggle next to Logging.
-
Click Apply.
-
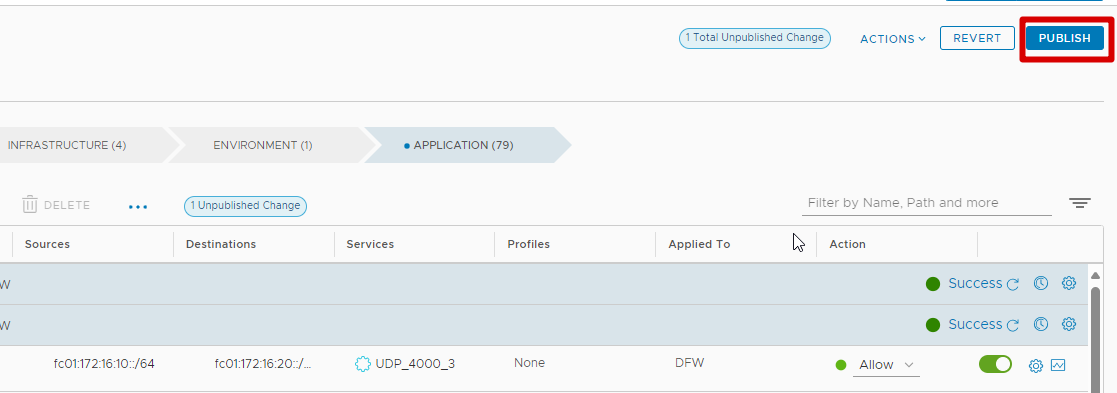
Click Publish in the top right to apply the changes.
Was this helpful?
Thank you!
We’d love your feedback
We really appreciate your feedback
Send this page to a colleague