On this page
Monitoring Juniper NetScreen
Overview
SecureTrack monitors Juniper devices for policy revision changes. For SecureTrack to show full accountability details (who made the policy changes and when the changes were made) and rule and object usage, you must also configure the device to send syslogs.
Prerequisites
Before you add the device to SecureTrack:
- SecureTrack and the monitored devices must be synchronized with the correct date and time, either manually or automatically. We recommend that you also configure the devices to resolve DNS queries.
-
Make sure that the Juniper device user account permission to run the following commands:
Netscreen
-
Retrieve revision
get config
get service pre-defined
get service <service>
get service group
get service group <group name>
get clock
get system
get hostname
get zone all
get zone
get zone id <zone_id>
exit -
Retrieve dynamic topology
get route
get route v4
get interface all
get interface <interface name> -
Virtual context
get vsys
enter vsys <vsys name>
JunOS
-
Retrieve revision
show configuration
show version
show uptime -
Virtual context
show logical-system
-
Dynamic topology
show configuration routing-instances
show route active-path
show interface
show vrrp
show bgp neighbor -
Provisioning
edit
configure
edit logical-system (for provisioning FW with logical system)Export versions of JunOS devices may not support SSH.
-
Recommendations
-
If you are adding the device as part of an HA cluster, each individual host IP should be added as a distinct standalone entity for monitoring purposes.
-
If the device is a standby member in a high availability cluster, monitor the device as a standalone device with usage analysis collection and topology disabled. This will prevent the standby member from appearing on the Map, and ensure that routing is correct.
Add a device
-
Select Juniper > NetScreen.
-
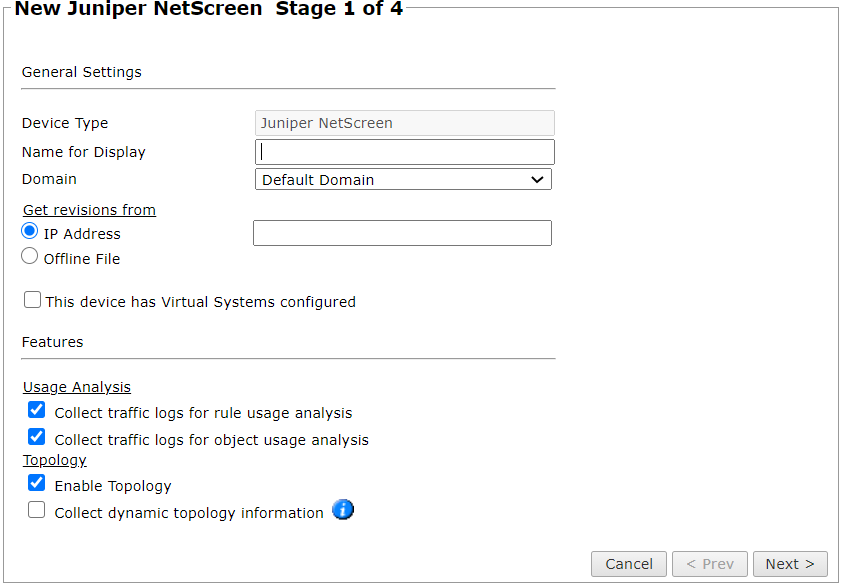
Configure the device settings:
- Name for Display
-
Domain: Available only if you have configured your system for managing multi-domains and All Domains is currently selected. Select the domain to which to add the device. The Domain can only be entered when adding a device; to change the Domain, you must migrate the device.
-
Get revisions from: One of the following:
-
IP Address: Revisions are retrieved automatically
-
Offline File: (If available) Revisions are manually uploaded to SecureTrack for Offline Analysis
-
-
ST server: In a distributed deployment, select which TOS cluster monitors this device (not shown in image)
-
This device has Virtual Systems configured: Select to enable adding and monitoring Virtual Systems.
If you have virtual systems, you can monitor clustered Netscreen devices. You can only do this when you first add the device to SecureTrack. To monitor a Netscreen cluster that has virtual systems, select This device has Virtual Systems configured and select Cluster.
-
Collect traffic logs for rule usage analysis is necessary for Rule Usage reports.
- Collect traffic logs for object usage analysis is necessary for reporting on unused objects and services in Rule Usage Reports.
Object usage analysis requires plenty of free disk space (depending on the number of gateways and the amount of traffic logs generated). If disk space is limited, you can configure SecureTrack to limit the number of days that data is kept.
We recommend that you enable SecureTrack administrative alerts, which notify you if there is low disk space on the server. When disk utilization exceeds 90% in the partition that has the database, SecureTrack sends an alert.
-
Enable Topology: Collects routing information for building the network Map.
Topology options for Advanced management mode are configured when you import managed devices.
- Collect dynamic topology information: Select if the device uses dynamic addressing (such as DHCP) or dynamic routing protocols (such as OSPF).
- Click Next.
-
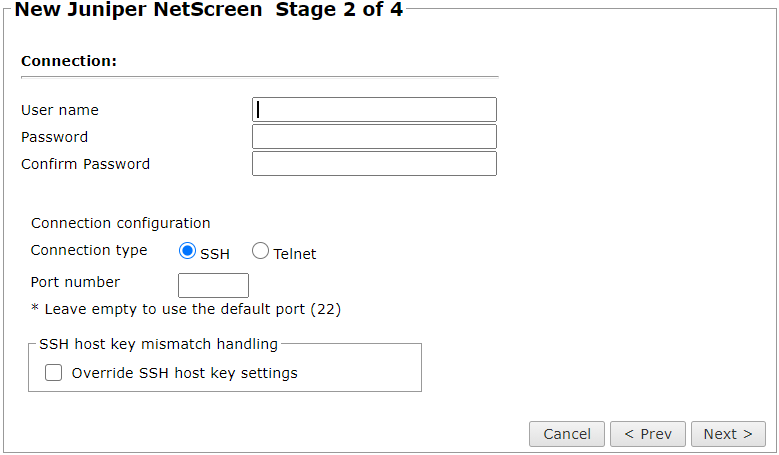
Configure the SecureTrack connection to the Juniper device, according to the parameters required by the device:
Make sure you have a user configured on the device with the privileges required by SecureTrack. See the prerequisites section for a list of required privileges.
-
Enter the authentication details (User name and Password) needed to connect to the Juniper device.
-
Connection configuration: Select whether to use SSH (preferred) or Telnet. To use default settings (recommended in most cases), leave the Port number blank.
The device must be configured to use SSH version 2.
-
- Click Next.
-
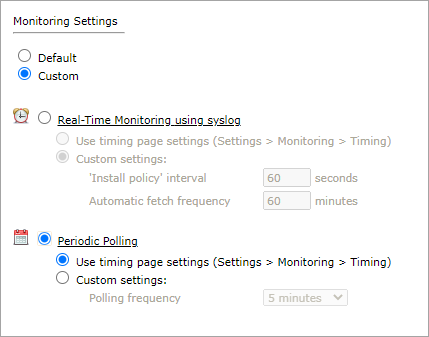
In Monitoring Settings, do one of the following:
- To use real-time monitoring and timing settings from the Timing page, select Default.
Otherwise, select Custom and configure the monitoring mode and settings:
-
Real-Time Monitoring: Applies only if syslogs Sending Additional Information Using Syslog) are configured. Select Custom settings and configure:
- 'Install policy' interval: When two or more Install Policy events for the same policy occur within this time interval, SecureTrack combines the events into a single Install Policy revision (Default: 60 seconds)
- Automatic fetch frequency: Frequency (in minutes) for automatic fetch
-
Periodic Polling, select Custom settings and configure the Polling frequency: How often SecureTrack fetches the configuration from each device.
If you select 1 day, you can then select the exact time (hour and minute) for the daily polling.
-
Click Next.
-
Save the configuration.
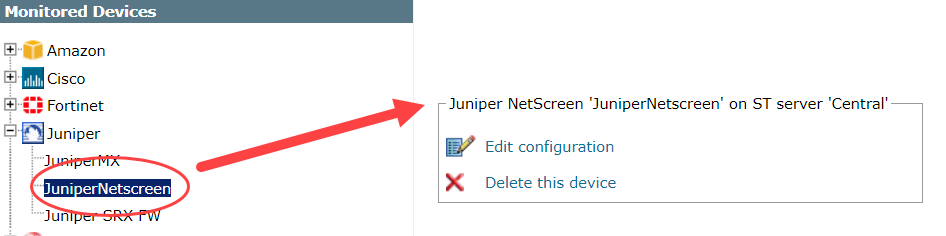
The Juniper device now appears in the Monitored Devices tree.
Configure a monitored device
After you add a device, further configuration options are available.
Options vary depending on your environment.
Example
-
Edit configuration: Use the wizard to modify selected device settings. See Add a Device in this topic.
-
Delete this device: Type yes to confirm that you want to delete the device.
How do I get here?
SecureTrack > Monitoring ![]() > Manage Devices
> Manage Devices
Was this helpful?
Thank you!
We’d love your feedback
We really appreciate your feedback
Send this page to a colleague