On This Page
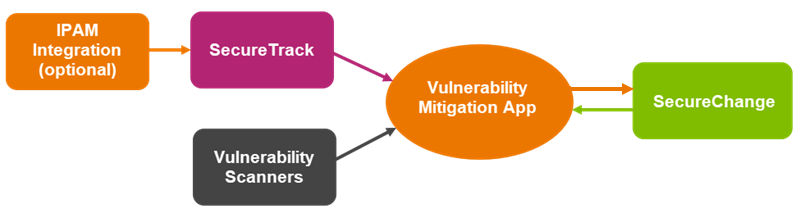
Vulnerability Mitigation App (VMA) takes input from the following sources:
- Vulnerability Management Systems (VMSs): These are external automated tools that identify network assets through available access and correlate their open ports and services to known network-based vulnerabilities associated with services. The VMSs automatically scan your network assets at fixed intervals and provide VMA with regular updates on the vulnerability status of your assets.
- SecureTrack: Provides VMA with access to network segments/zones and the rules of SecureTrack managed devices to calculate context for the vulnerabilities detected.
The input provided by the VMSs and SecureTrack are what enable VMA to provide you with a better understanding of the vulnerability status of your assets, such as:
- The total number of vulnerable assets, rules and underlying services that provide access to those assets (Dashboard)
- The vulnerability breakdown across zones (Zones menu).
- Trends over time that can help reveal whether your vulnerability mitigation efforts are improving.
VMA correlates rules by the vulnerabilities’ services. Only rules that match the source or destination AND one of the services are considered vulnerable and correlated to VMA.
With this knowledge, you can then choose an appropriate course of action to minimize the risk to your network:
- Prioritize rule removal for mitigation
- Prioritize asset decommission for mitigation
- Block access to the assets.
- Prioritize vulnerability patching remediation
- Share policies that require modification to ensure mitigation
If there are any errors when VMA correlates data from SecureTrack, an alert is displayed in the application, and a notification is added to the Notifications menu (click the  button in the title bar).
button in the title bar).
VMA's output is in SecureChange. If you have assets that need to be mitigated, you can select them in VMA and open a server decommission ticket or group modification ticket. These tickets are then communicated from VMA to SecureChange.
After the ticket is submitted, VMA pulls the ticket info from SecureChange, enabling you to track the ticket status directly from VMA.
These data correlation and vulnerability mitigation capabilities will enable you to minimize the security risks to your network, provide you with much needed context and visibility, and allow you to quickly and efficiently mitigate your network-based security risks as soon as they are detected.