On This Page
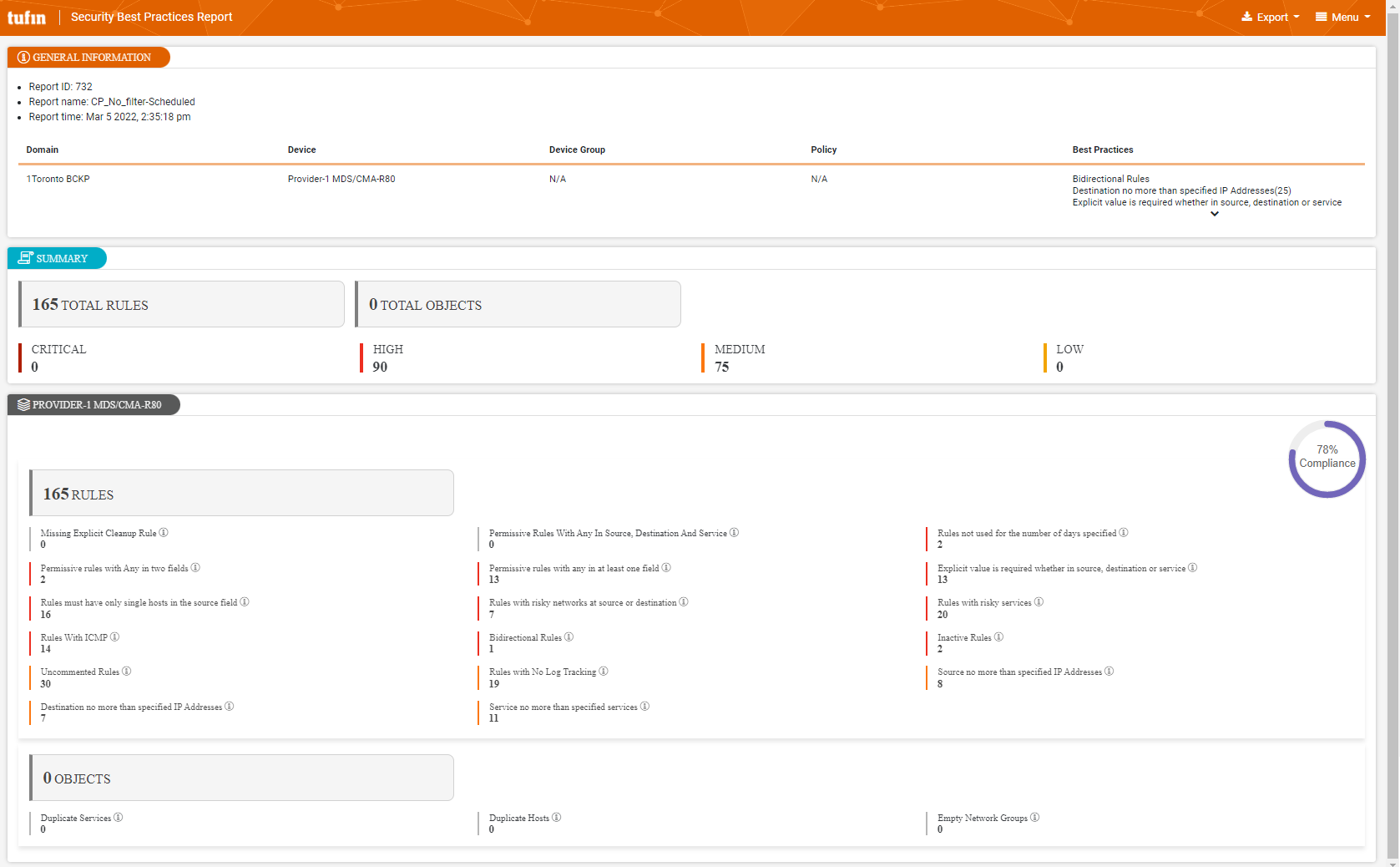
Security Best Practices Report
Overview
The Security Best Practices report provides the organization with the ability to ensure that security controls are based on common security best practices and to detect best practice failures. It lists all the rules that violate each best practice.
This report enables you to:
-
Identify the locations of risks across your network and which devices are most impacted
-
Prioritize rule optimization and remediation
-
Ensure awareness of the state of your network for audit purposes
Security Best Practices report supports the PCI DSS v4.0 standards.
What Can I See Here?
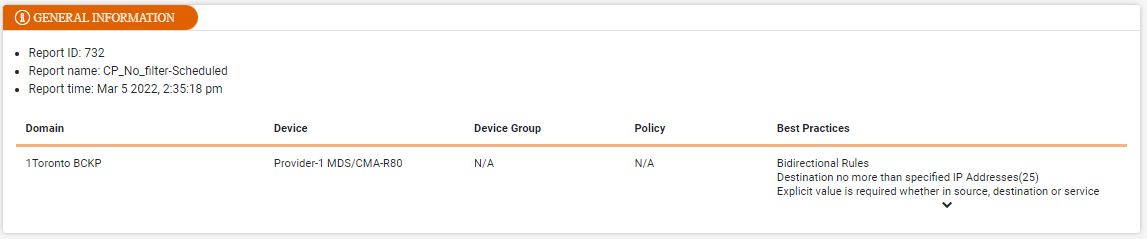
General Information
This section shows information such as report ID, name, time, and the domain details including the best practices selected during report creation.
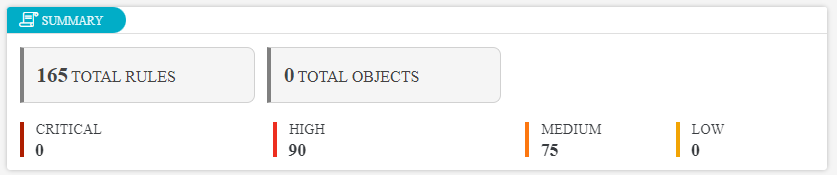
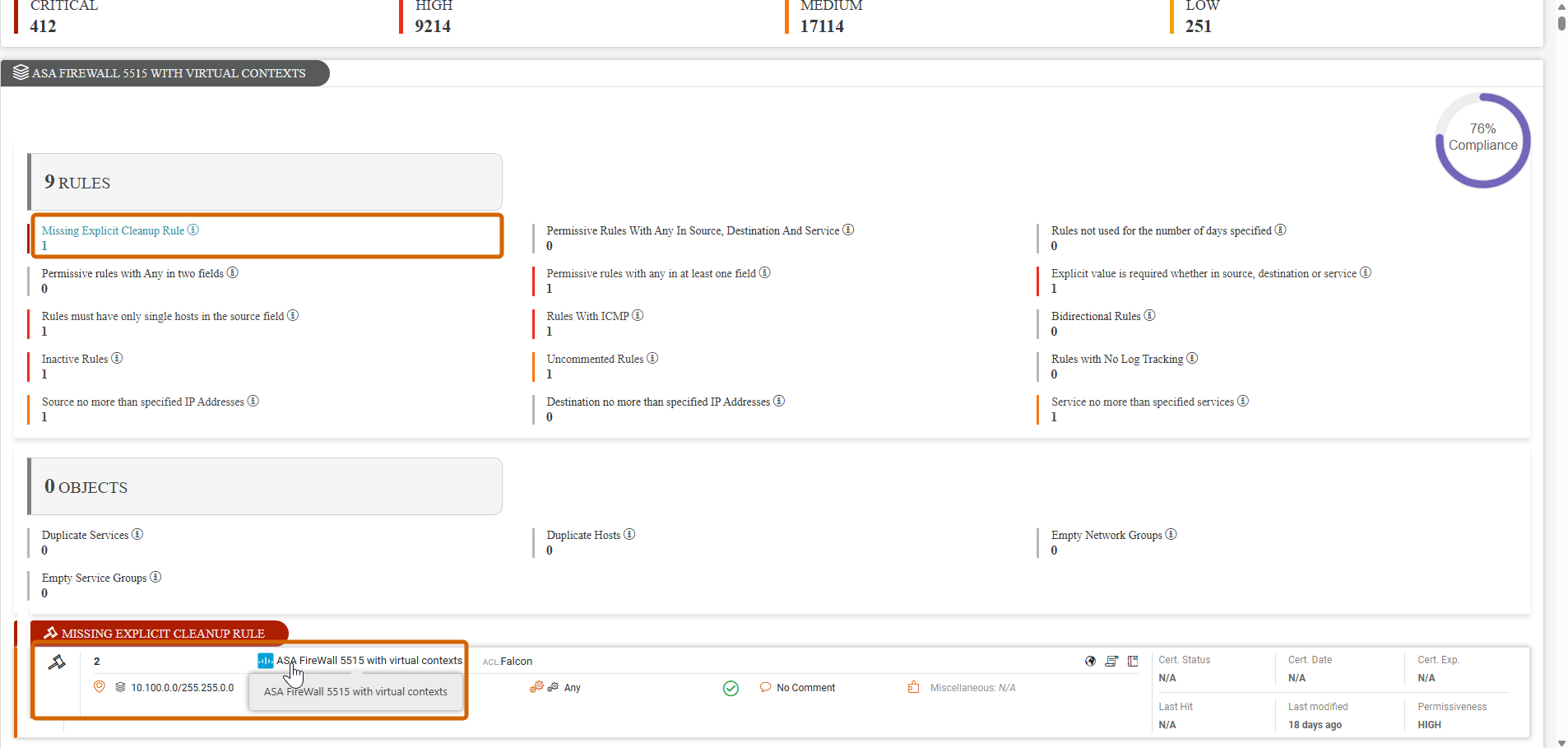
Summary
This section shows the total number of rules and objects with the breakdown by severity.
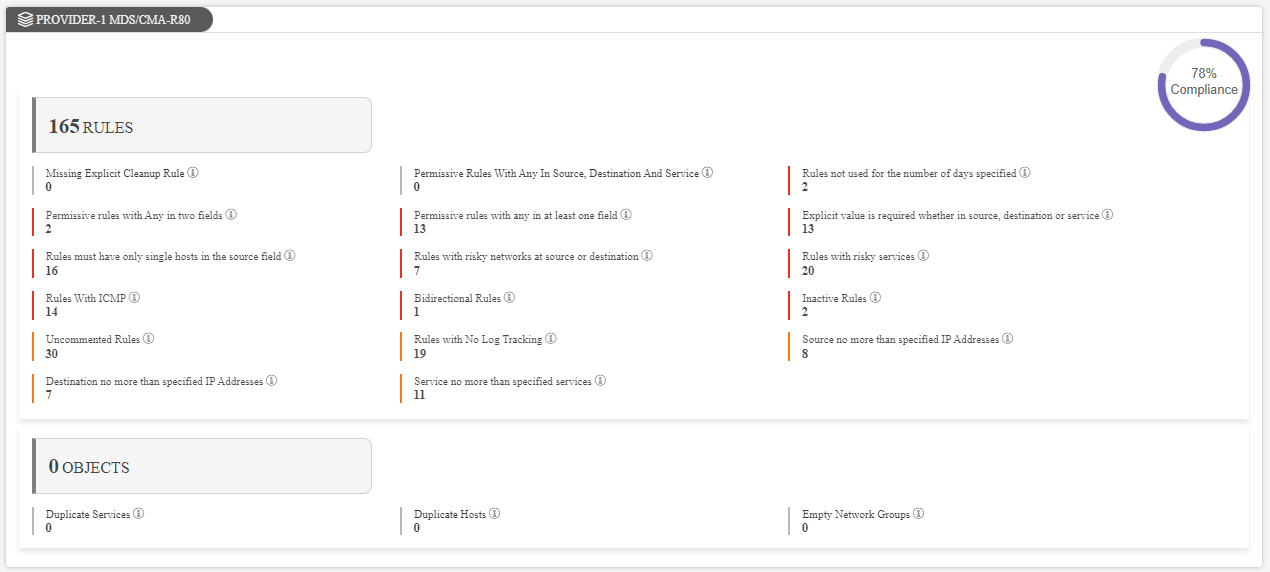
Rule and Object Best Practices per Device
These sections show the best practices that you selected when creating the report and the number of rules or objects that violate the best practices. The color of the bar next to the best practice indicates the severity of the violation:
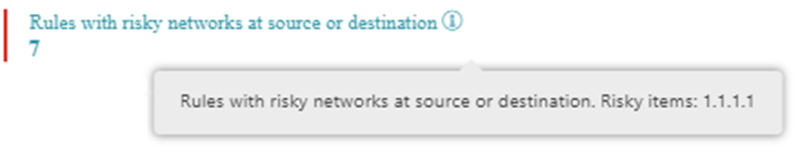
Hover over a tooltip to see an explanation for the best practice:
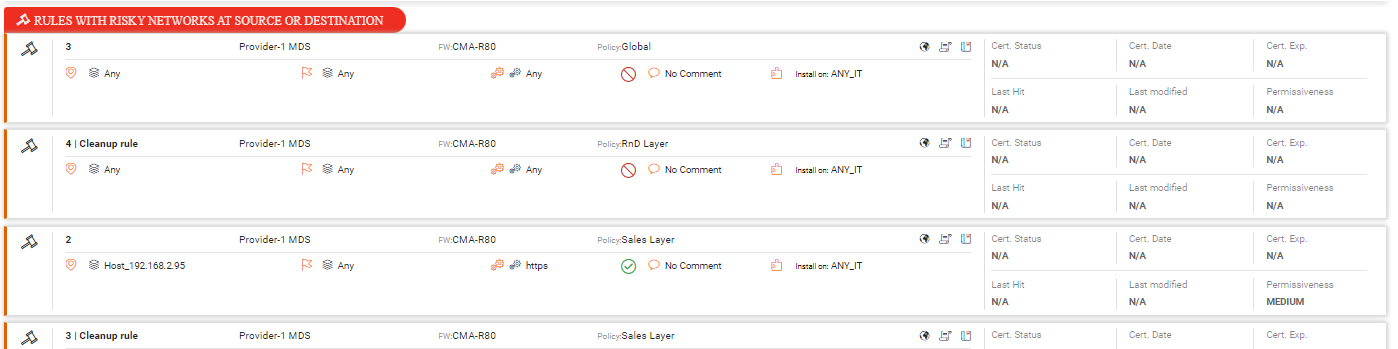
Click a best practice to see the violations details in a new section:
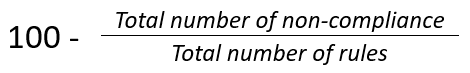
This compliance measurement shows the overall percentage of compliance for all best practices.

It is calculated as follows:
Rules
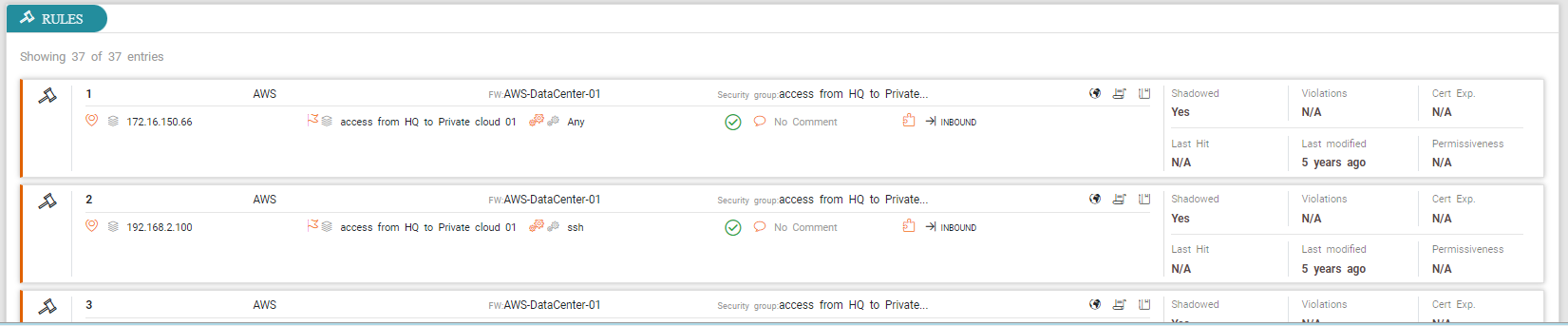
The rule cards show all information for rules resulting from the TQL search.
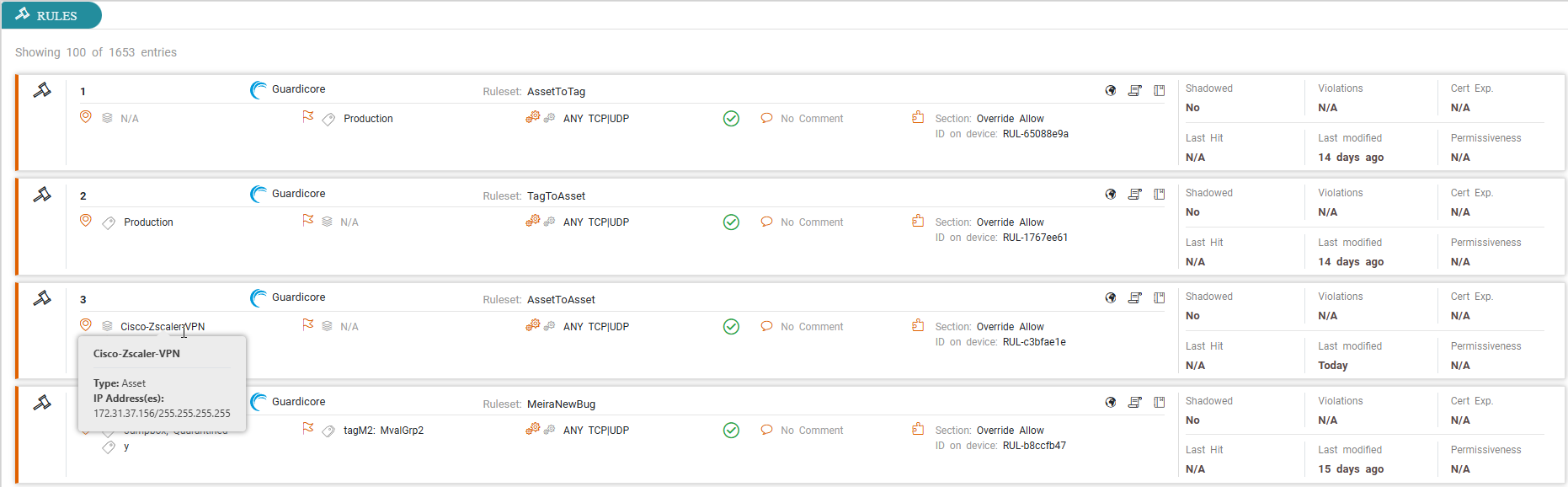
Rules for Guardicore devices
When Guardicore devices are selected, the rule card shows the tags and tag groups configured for the device. Hovering over the tag shows both the tag key and tag value.
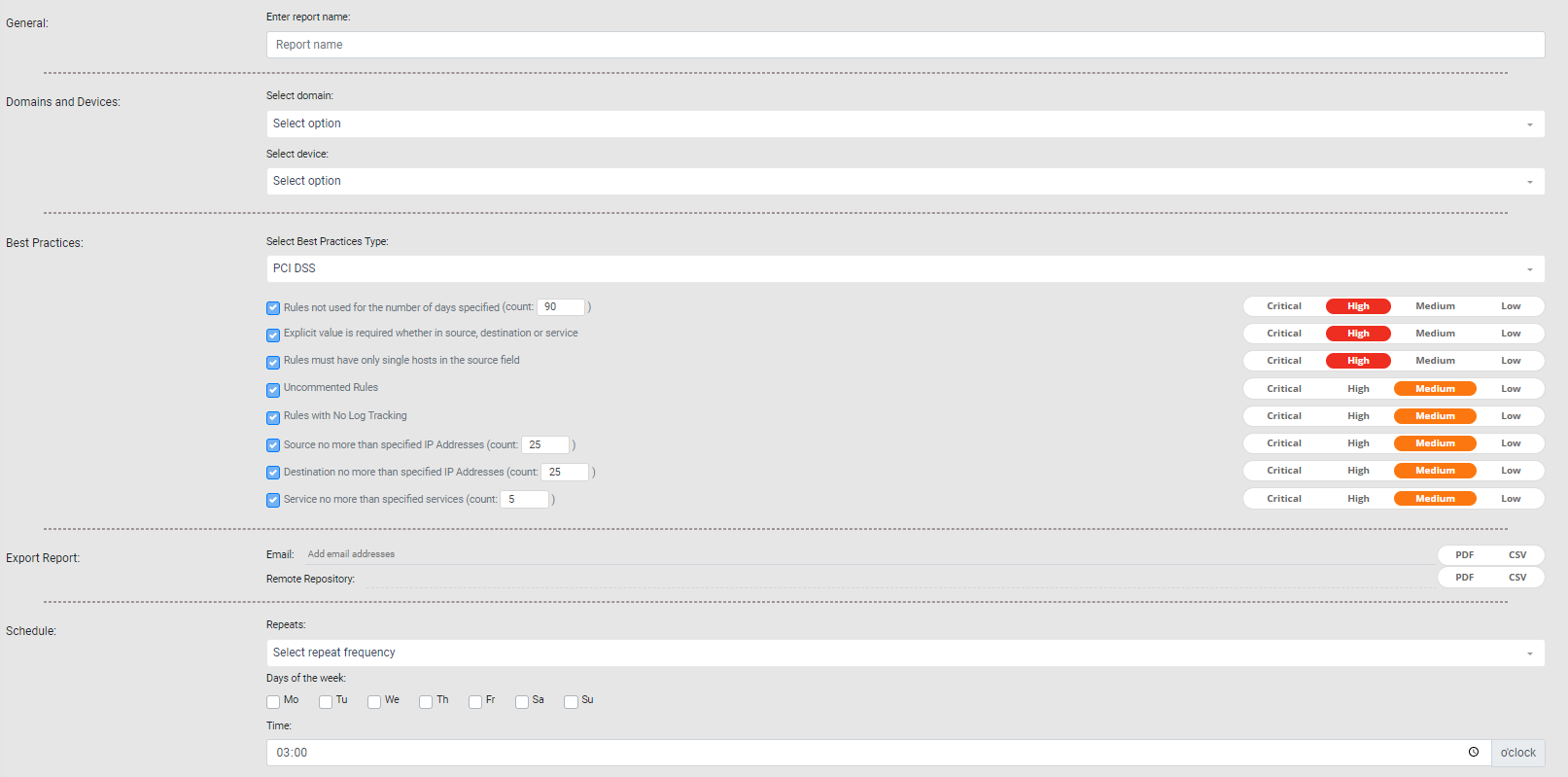
Create a Security Best Practices Report
Prerequisites
-
In the Settings > General page, the administrator must configure the outgoing SMTP server and the remote repository.
Procedure
-
From the Create (
 ) menu, click Security Best Practices.
) menu, click Security Best Practices.The Setup page for the report appears.
-
Complete the report fields:
-
General: Report name.
-
Domains and Devices: Select a domain and one or more devices or device groups.
-
Best Practices: Select the Best Practices Type. For best practices that require a value, you must supply the value AND select the check box. If not selected, STRE ignores the best practice.
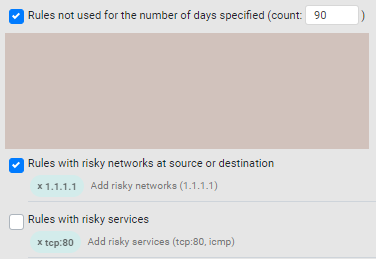
<tcp/udp>:<port>formaticmp
STRE only supports the following options for the risky services field:-
Export Report:
-
Email: Specify the recipients for notification emails. Press Tab or Enter to separate multiple email addresses.
The email message includes a link to the report in STRE.
Select the format of the report to include in the email as an attachment, as PDF, CSV, or both. Reports larger than 4 MB are compressed as
.zipfiles. -
Remote Repository: STRE can export reports using SFTP. Specify the report format - PDF or CSV.
If the report finished successfully, you can verify that the new files appear in the Reports Folder path, in the remote repository, configured by your administrator (see Send Reports Using SFTP).
-
- Schedule: Configure the following:
- Repeats: The frequency at which the report runs: Daily, Weekly, or Monthly.
- Days of the week: Available for Weekly and Monthly frequencies.
For Weekly, runs the report on each selected day at the specified time. For example, if you select Monday, the report runs every Monday.
For Monthly, this is one of two scheduling options. Runs report on the first occurrence of the selected day of the week in the month at the specified time. For example, if you select Monday, the report runs on the first Monday of the month.
- Calendar Month: Available only for Monthly frequencies. This is the second monthly scheduling option. Runs report on the 1st or 15th of the calendar month. Reports based on calendar months run automatically at midnight.
- Time: The time at which the report should run.
-
-
Click one of the following:
 : Saves the report. The Saved menu lists all saved and scheduled reports.
: Saves the report. The Saved menu lists all saved and scheduled reports. : Runs the report. After a report runs, you can view the results in the Repo menu.
: Runs the report. After a report runs, you can view the results in the Repo menu.
Severity Settings
The report builder provides a default severity setting for each of the available Best Practices checks. Severity settings are primarily intended to help prioritize the security checks included in the report results. All severity settings are suggestions and can be modified to suit the preferences, risk tolerance, and needs of your organization.
Whether you are using a group of checks listed under a specific regulatory template (i.e. PCI DSS, ISO 27001, etc.) or using the complete collection of checks for general risk management, the severity ratings can be used to convey four levels of urgency.
-
Critical — Failure to comply represents a material violation of widely accepted security best practices that significantly increases the likelihood of unauthorized access, regulatory exposure, or operational disruption. These findings typically reflect high-impact misconfigurations or behaviors that create clear and actionable exposure and should be remediated immediately.
-
High — Indicates a significant deviation from established security best practices that elevates organizational risk. While not necessarily indicative of an imminent compromise, these issues meaningfully weaken the security posture and should be addressed promptly to prevent escalation or downstream exposure.
-
Medium — Reflects conditions that degrade rule governance, visibility, or alignment with security principles. These findings do not usually pose an immediate threat but may increase risk over time, hinder auditability, or complicate investigation and response efforts if left uncorrected.
-
Low — Represents minor configuration inconsistencies, procedural gaps, or optimization opportunities. Addressing these findings improves policy hygiene, reduces "noise" in audits, and supports long-term maintainability, but they generally have minimal direct security impact.
Export Reports from Local Repository
After creating a report, export it to any supported format from the Repo menu.
-
CSV: Use to create your own reports based on the specific data from the report configuration.
-
PDF: Use to export as a ZIP file.
-
If the report exceeds 250 rules, the ZIP file includes multiple PDFs, each including up to 250 rules. The name includes the sequence in the format <num> of <total_reports> to indicate the order. For example, 1 of 3.
-
A single report comprising multiple PDFs can include a total of 6000 rules. To increase the limit, contact Tufin Support.
-
Open Rule in SecureTrack
When viewing the report online, you can go directly from a rule in to the corresponding rule in SecureTrack.
Expand the results, and click the rule ID or rule name to open the rule’s Overview tab in Rule Viewer.